Most organizations will use Windows devices as their backbone for work. While management is most likely already familiar with Azure AD as it is an essential service tool, it is equally as likely that you have never heard of it before, or at least you may be unaware of what the functions and role of Azure are, read on to find out more.
The main purpose of Azure Active Directory (Azure AD) is to be used as a database by businesses to keep track of user information, access privileges, and stock of devices. Businesses can make policies in Azure AD to set rules for their users and track sign-ins and what they are accessing.
This article will cover the basics of Azure AD, what it does, why we use it, and who can make the most out of it. This guide will cover the difference between Azure AD and Active Directory. Despite being a Microsoft service, both Windows and Mac can use Azure in a browser.
Content List – What this article will cover
- What is Azure AD, and why do we use it?
- My thoughts on Azure AD
- How to change User access settings
- Who is Azure AD made for?
- Conclusion
What is Azure AD, and Why do we use it?
To start with, Azure Active Directory or “Azure AD” is a tool created by Microsoft primarily based in the cloud; it functions as a service primarily for admins that lets you manage access between people and software. It has become one of the more critically used services that Windows has access to ever since its predecessor “Active Directory,” released in 2000. Azure AD is a similar but different version of regular AD, allowing staff access to internal and external resources that they wouldn’t be able to without AD. Internal resources, for example, include things on the intranet or local area network— this can include any apps your company makes your devices mandatory and any cloud-based apps your organization creates.
Active Directory functions differently from Azure AD in a few ways and is not necessarily a replacement. One example of this is Active Directory, which is suitable for managing “on-site” apps and software and allows its users to access any resource they need for the job on their devices. In contrast, Azure is better for anything involving the cloud and controlling user access to software and accounts. The way that apps are “managed” is by allowing users to configure different sign-in requirements around specific apps; for example, you can allow “Single Sign Ons” (SSO) for some apps or multi-factor authentication for others.
Both Azure AD and Active Directory act as a database containing users’ information, such as their login credentials, i.e., username and passwords; you can also find user details in Microsoft 365 admin center. While they cover different fields, both will show a database with a list of people and monitored equipment, for instance, how many devices are inputted into the system. It also showcases the users and their privileges, including their access to specific software and sites. Depending on the size of the business or organization, this list could contain tens or hundreds of people, each with its list of details and access limits.
Azure AD is a service tool that will affect most of the content, and the software you will use as an admin will set access limits for individuals. Azure does this by checking your credentials are what is on the database and if you have access or not. If you cannot access something, you will need to contact an admin to get around it. However, this is likely because you don’t have the permissions for it, which is typically done for a reason.
Azure AD options
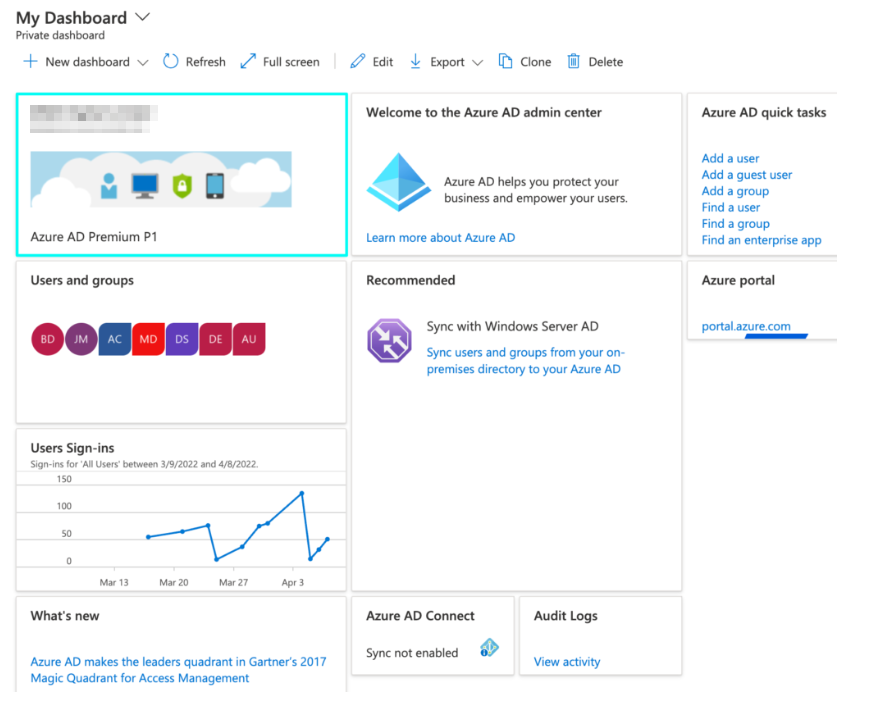
Below I have compiled some of the places you can go on your organization’s Azure portal. These can all be found by clicking on your business, then Azure Active Directory, where you can click on where you want to go by going to the appropriate option.
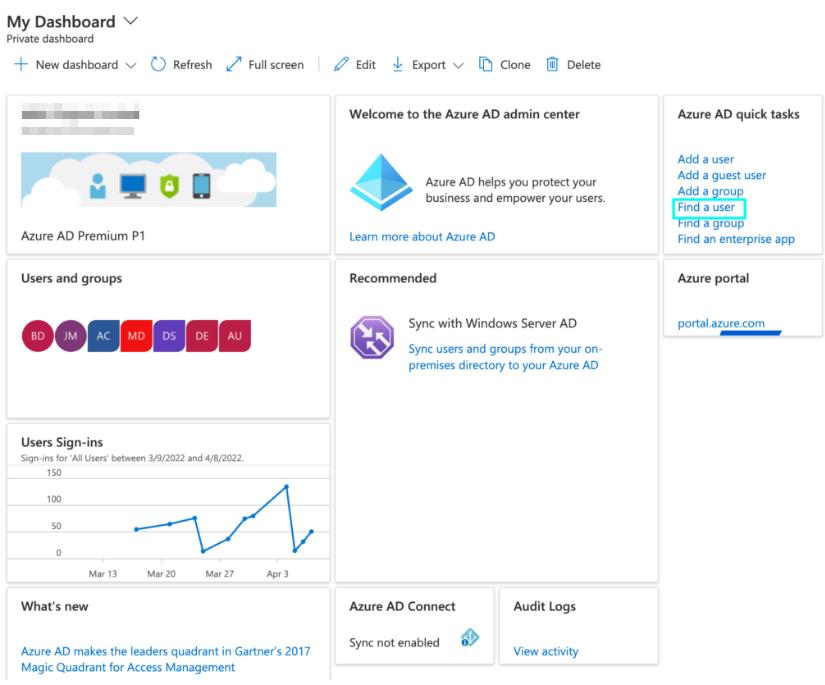
Dashboard
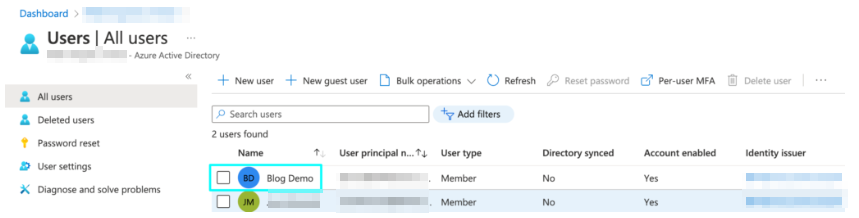
User List
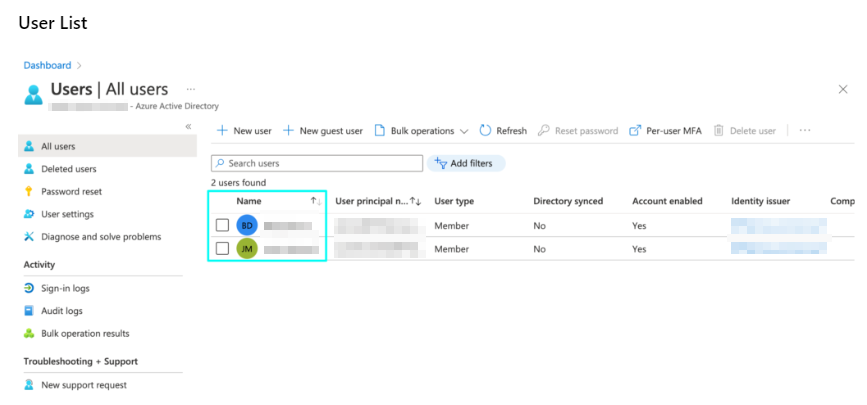
This is where the list of users in the business can be found; for this blog, our demo business only has two people, but your business may contain dozens more. You can find a user’s information here by clicking on their account.
Azure AD All Services page – Identity
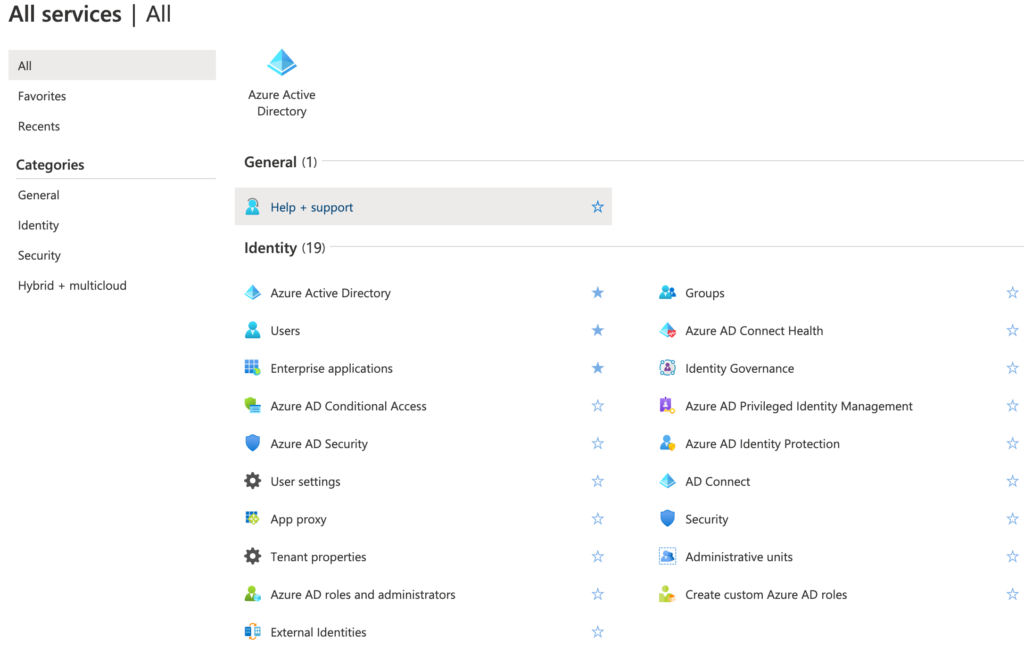
This is where you can seek options to seek individual users. “Users” allows you to find a list of people, and “Groups” shows any groups you or the business have created with specific Microsoft software. “Conditional access” is where you can create policies for setting rules over your organization that will affect what users can do.
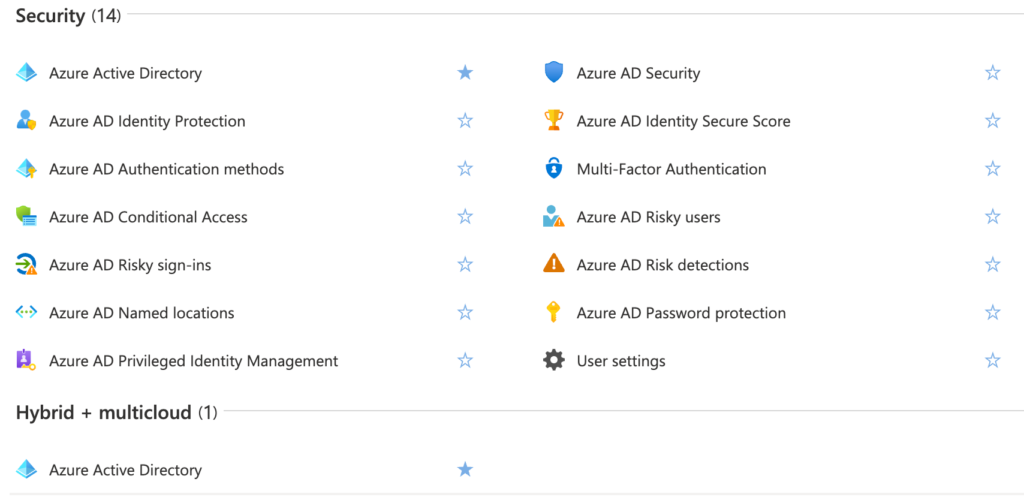
Azure AD All Services page – Security and Hybrid + multi-cloud
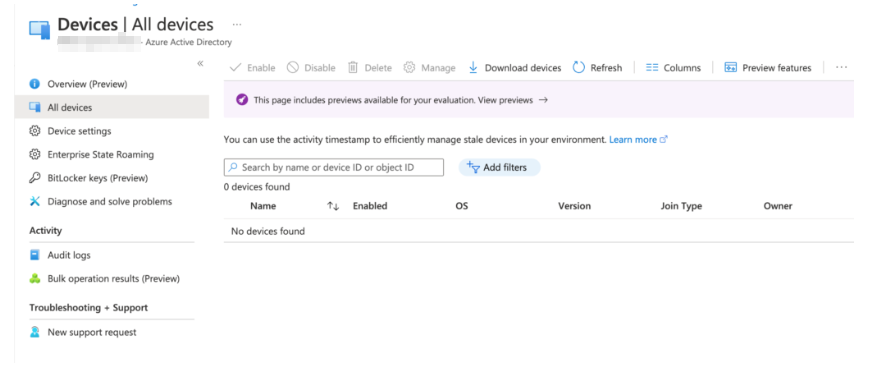
Azure AD Devices page
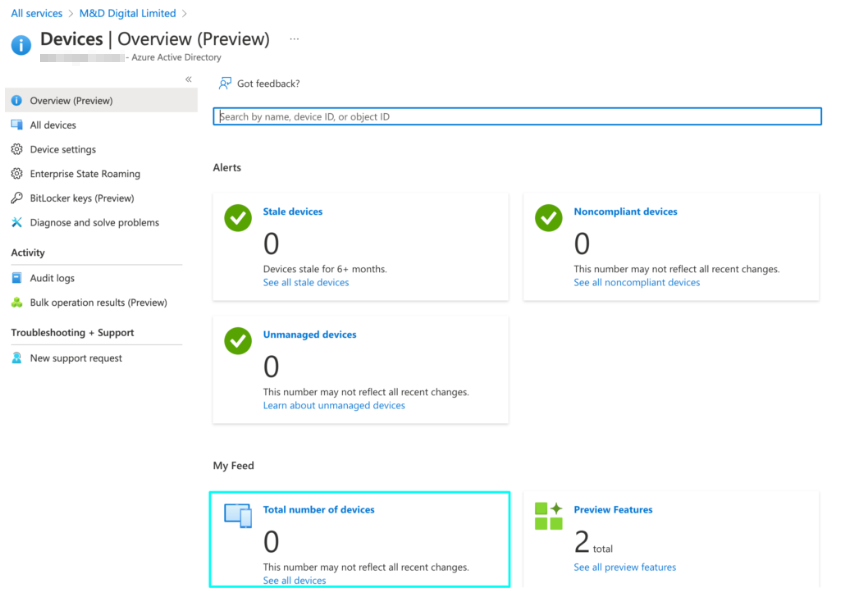
Here you can find the number of registered devices for your business. For any other business, the number will be much higher than zero; this is because it is a test business account. You can show a list of devices by clicking on “all devices.”
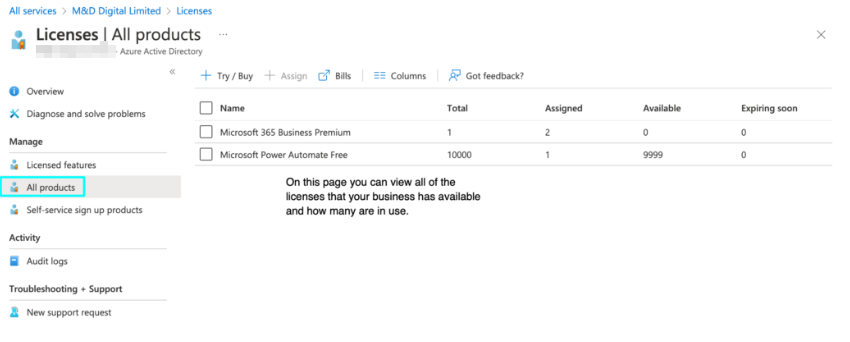
Licenses

How to change user access settings
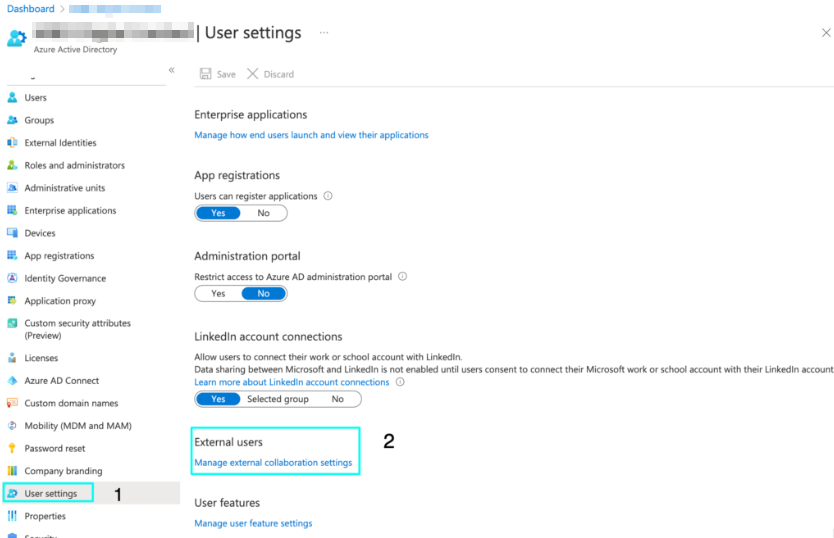
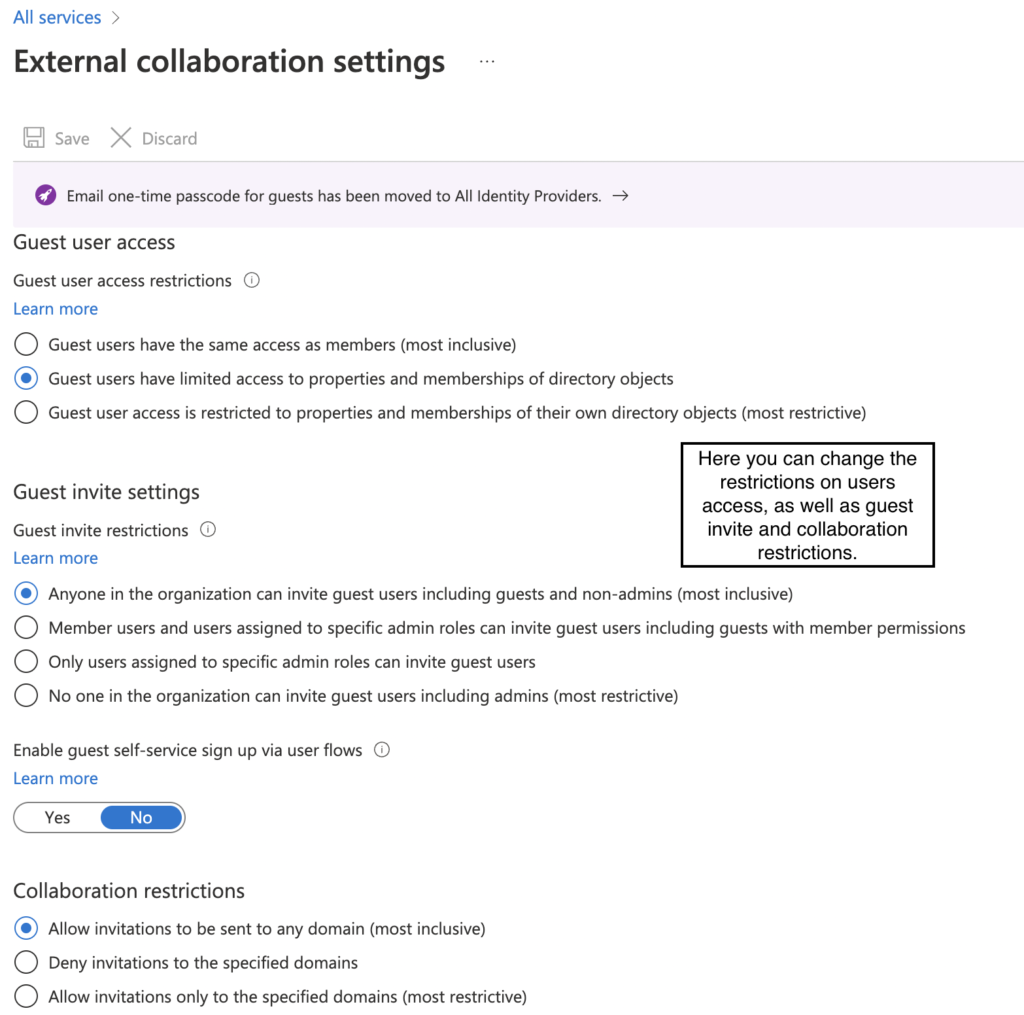
You can change the user access settings by going to your business portal, “Azure Active Directory,” then scrolling down to “User settings,” then under “External Users,” click “Manage external collaboration settings.” This feature lets you set access restrictions for guest accounts.
You need to view your account role to see what level of access you have.
- You can do this by going to the dashboard and clicking “Find a User.”
- Next, you need to find an account in the user list.
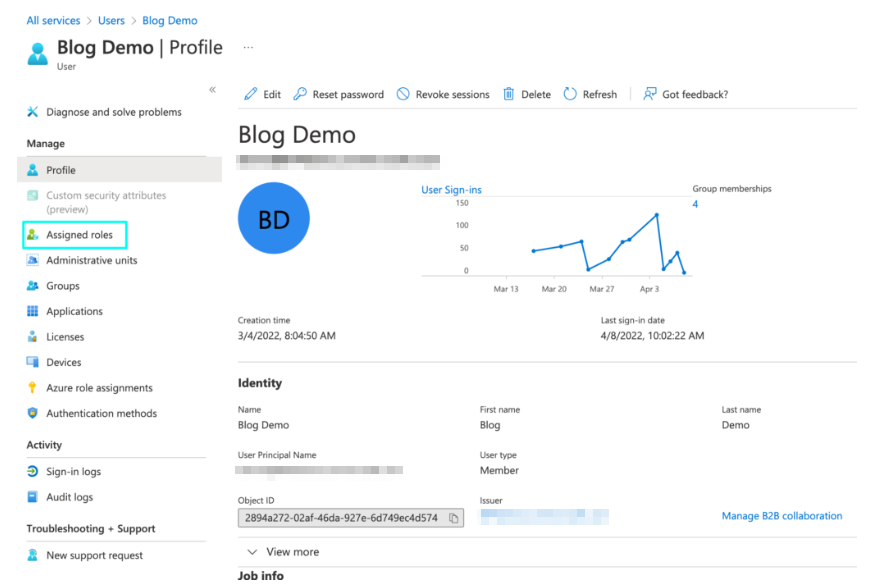
- You need to click “Assigned roles,” which will bring a page showing what level of access your account has.
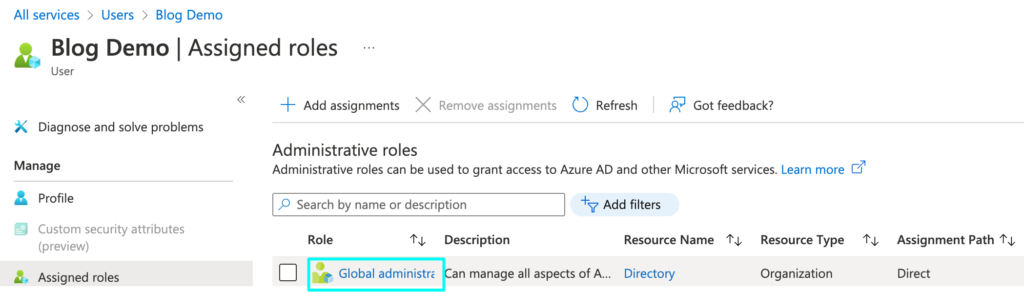
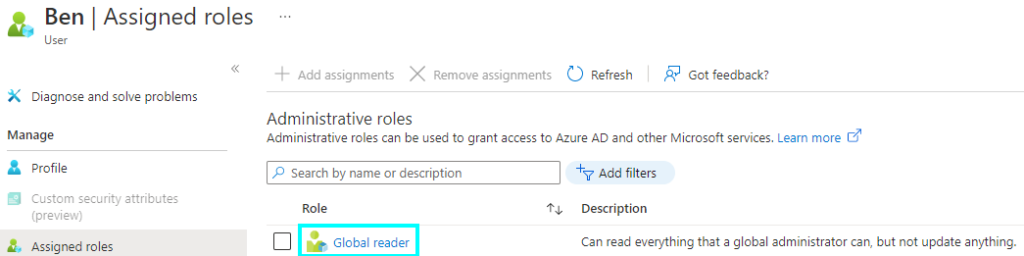
Here I will show two different levels of account access with a user from another business’s Azure AD; I will do this because this test account doesn’t have two different levels of access. To view their access privileges, you will need to view their accounts.
User from demo business
User from another business
Who is Azure AD made for?
While Azure AD can technically be used or at least viewed by most people, there are a few groups of people that can benefit and get the most from Azure AD and Active Directory, a few, for example, include App developers, Admins, as well as Azure subscribers, as well as Microsoft 365, Office 365 and Dynamics CRM Online subscribers; each of these can make use of Azure AD in their way, but all can view the database if they have the correct credentials. Below are a few ways that people might use Azure AD.
| Who can use Azure? | What do they do with it? |
| App Developers | If you are developing an application, you could use Azure AD and its many functions to help with parts of its development; for example, you could add the function “Single Sign-on,” which will allow users to sign in with any existing credentials. Or you could make use of an “API” or Application Programming Interface, which lets the developer create the app with more personal touches by making use of data that the business has on people. |
| IT Admins | An IT admin could use Azure to go more in-depth than other people as they would go further into the management side. Azure can also benefit admins because you can access everyone’s information and what software and services people can access. You also have access to app resources; this will change depending on what your business wants to have access to. This means that admins can choose to set SSO or MFA requirements for specific software. With the access that admins have, they can protect user identity by managing their credentials. |
| Office 365, Azure, and CRM Subscribers | If you are subscribed to any of these, you use Azure AD. Anyone subscribed to these will be listed on Azure AD’s database. Once you subscribe, you can begin to access your Azure details. You can access Azure and view your profile to edit specific pieces of the ‘Identities’ page. However, you can’t change your password here. |
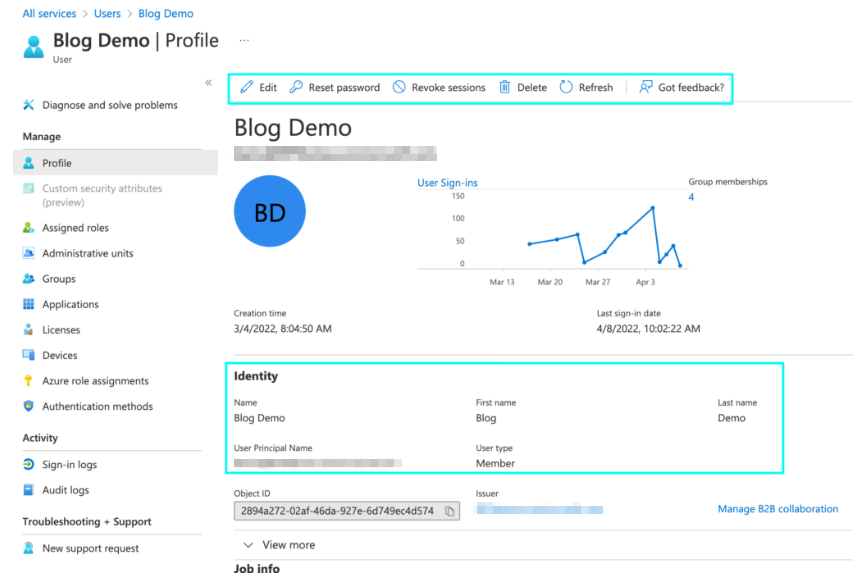
Once you’re on the user account, you can edit some of the information, reset the password, etc., and the basic information on the page, like how your name will be listed on the page.
My thoughts about Azure AD
I have taken the time to look through Azure AD to find where specific options are located; I have found that Azure can be navigated efficiently, but it could take time for unfamiliar ones. The benefits of Azure AD go further than allowing users to view account details but lie in the wealth of features that the business can take advantage of, like the Identity and Security options.
These both contain a large number of options that admins can use to manage the analytical and information side of the business easily; this is why Azure is second to none when it comes to business information database options, and it can be used on more than just desktop use, as you can run it on mobile, iOS, Mac, and more.
I also asked on the Microsoft forums what the benefits of Azure were in the position of a new business owner; a Microsoft Agent replied to me by saying the following.
Hello Dominic,
The ways how your business can benefit with Azure Active Directory depends on your business’s working model and its purposes. Generally, Azure AD is a cloud-based identity and access management service. This service helps your employees access external resources, such as Microsoft 365, the Azure portal, and thousands of other SaaS applications. Azure AD also helps them access internal resources. These are resources like apps on your corporate network and intranet, along with any cloud apps developed by your own organization.
Igor Tarasuga MSFTMicrosoft Agent |
Moderator
Conclusion
Azure AD and Active Directory are used as databases to store, manage and check user information and access privileges. It can be viewed by any Windows 10 user with at least a subscription to Office 365, although only an admin should be able to edit a user’s details. Depending on what you want, Azure AD can offer its users many different features and functions, although this will vary by what access you have.
Thank you for taking the time to read through this article; if you have any thoughts about it or would like to critique it, you can leave feedback for us. If you have any other questions, you can contact our friendly staff, or you are free to check out our plethora of other articles and guides for all of your tech needs.
